Network Security
Web Application Firewall

Applications that provide services to end-users can be vulnerable to many threats. Although many of these threats can be prevented by application developers, this often is outside the web site owner's control. A web application firewall (WAF) provides a layer of control between end-users and applications.
A WAF filters all application access, inspecting both the traffic towards the web application and the response traffic from the application. By securing both the application infrastructure as well as the application user, a WAF complements traditional network firewalls, which are not designed to protect at this granular level.
Threat Vectors
Applications can be vulnerable to many threats that are not detected by regular network firewalls. The impact of these attacks can be quite severe. Here are some examples:
Injection
SQL Injection Attacks use a Web form or other mechanism to send SQL commands or commands containing SQL special characters. By sending these SQL commands, the attacker can trigger the backend SQL database to execute the injected commands and allow unauthorized users to obtain sensitive information from the database.
Cross-site scripting (XSS)
XSS attacks exploit a Web server that does not validate data coming from another site. XSS can enable the attacker to obtain sensitive information, or to compromise a Web server.
Sensitive data exposure
If Web applications do not protect sensitive data such as credit card numbers or Social Security Numbers (SSN), attackers are able to conduct identity theft, credit card fraud, or other crimes.
Cross-site request forgery (CSRF)
CSRF attacks force a user to send an HTTP request, including the victim's session cookie, to a vulnerable web application. To the vulnerable web application, this appears to be a legitimate request coming from the victim.
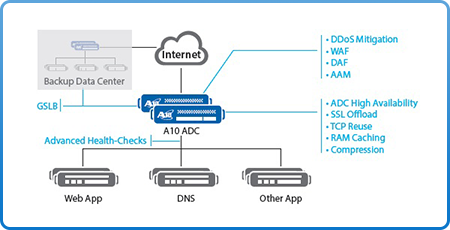
A10 Thunder and AX Series Web Application Firewall
The A10 Thunder and AX Series ADCs include a full featured, ICSA Labs-certified Web Application Firewall that blocks web attacks before they can reach vulnerable applications. Deployed as a proxy in front of web servers, Thunder ADC inspects web requests and responses and can block, sanitize, or log malicious activity. The WAF enables a full defense stack with other A10 security mechanisms in order to protect web applications, ensure against code vulnerabilities and prevent data leakage; this aids in regulatory security compliance, such as Payment Card Industry (PCI) Data Security Standard (DSS) requirements. A10's WAF feature is designed to recognize many of today's threats, with flexibility to customize checks for emerging threats. The WAF is tightly integrated with other A10 security features within the Advanced Core Operating System (ACOS). Instead of integrating 3rd party WAF code, as many other vendors do, A10 has developed the WAF specifically for ACOS. This approach results in a highly scalable and high performance security solution which is simple to configure.
